In an era where most businesses rely heavily on the cloud for running critical workloads, security is no longer just a feature — it’s a necessity. Cloud environments offer incredible flexibility, scalability, and cost-efficiency, but they also introduce a new set of risks. Misconfigured access policies, open APIs, insecure storage, and weak identity management are just some of the vulnerabilities that cybercriminals can exploit. To stay ahead of these threats, incorporating pentest cloud services into your security strategy is essential.
At Opsio Cloud, we understand that cloud security is more than just compliance — it’s about building resilient systems that can stand up to the most sophisticated attacks. In this blog, we’ll dive deep into what cloud penetration testing is, why it’s critical, how it works, and how your organization can benefit from a well-designed pentest strategy.
What Are Cloud Pentest Services?
Cloud pentest services (penetration testing) are a specialized form of ethical hacking that targets cloud-based infrastructure, applications, APIs, storage, and identity systems. Unlike traditional pentests that focus only on on-premises servers or networks, cloud pentesting simulates real-world cyberattacks in a dynamic, distributed environment.
A typical cloud pentest aims to:
- Discover Misconfigurations – Identify public storage buckets, weak firewall rules, or permissive IAM roles that may expose sensitive data.
- Test API Security – Verify that cloud APIs are not exposing data, are protected from injection or improper authentication, and are properly rate-limited.
- Probe Networking Layers – Check for open ports, insecure virtual networks, or insecure network design within virtual private clouds.
- Validate Identity & Access Controls – Analyze role-based access control (RBAC), privilege escalation paths, and identity mismanagement.
- Evaluate Application Security – Test cloud-native applications (microservices, serverless functions, containers) for vulnerabilities like injection, insecure deserialization, or broken authorization.
Why Pentesting Your Cloud Environment Matters
1. Cloud Misconfigurations Are a Major Risk
One of the leading causes of cloud data leaks is misconfiguration. While cloud providers offer strong core security, customers can accidentally leave resources exposed if they don’t configure access controls correctly. Pentest cloud services catch these mistakes proactively — before attackers can exploit them.
2. Increasing Sophistication of Cloud Attacks
Attackers are becoming more skilled at targeting cloud environments. They use automated tools, breach-as-a-service platforms, and advanced techniques to exploit gaps in APIs, identity, or infrastructure. Conducting regular penetration testing helps you stay one step ahead of these evolving threats.
3. Reducing Risk to Sensitive Data
Cloud applications often house highly sensitive data — customer information, financial records, or proprietary business assets. A successful breach can lead to large-scale data loss, reputational damage, and regulatory penalties. Pentesting helps secure these assets by identifying risks before they become real problems.
4. Compliance and Audit Requirements
Many industries demand regular security assessments to comply with standards like ISO 27001, PCI DSS, HIPAA, or SOC 2. Cloud pentesting provides the concrete proof that your systems have been tested under real-world attack scenarios, satisfying auditors and regulators.
5. Strengthening Your Incident Response
A pentest not only identifies vulnerabilities, but also helps you test how well your team responds to security incidents. By simulating attacks, you can measure detection speed, understand your response procedures, and fine-tune your incident playbooks.
How Cloud Penetration Testing Works
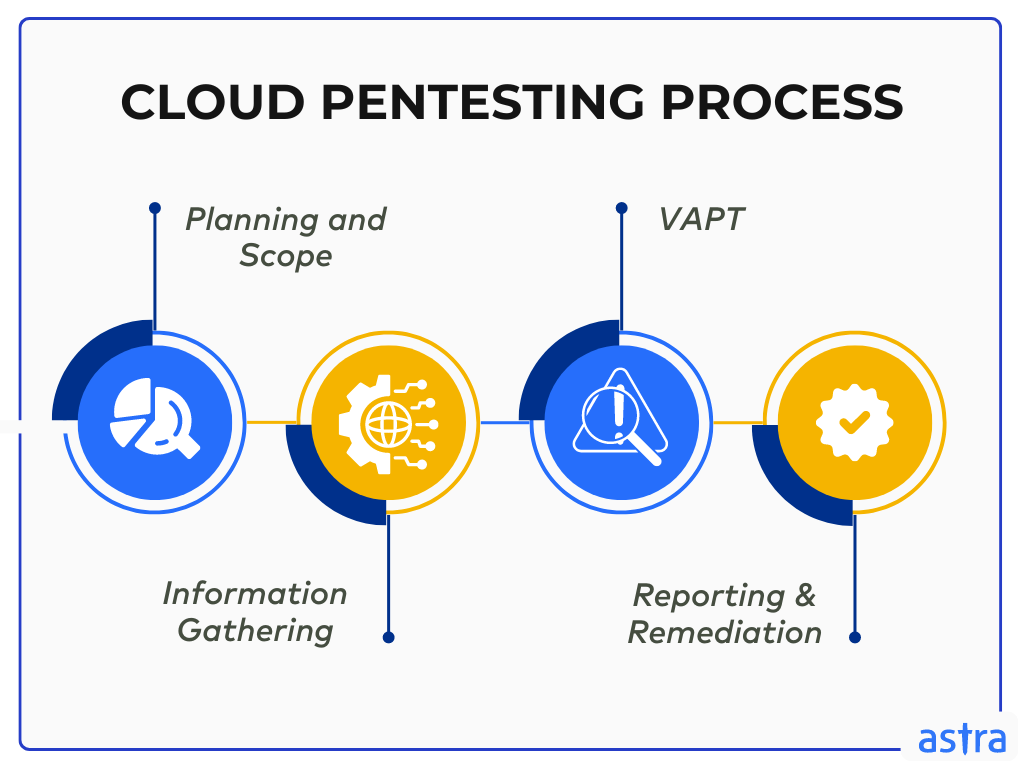
Step 1: Scoping and Planning
First, the pentest team collaborates with your security and DevOps teams to define the scope. Which services will be tested (VMs, storage, APIs)? What is the threat model? What rules must testers respect? Clear scoping ensures that the pentest delivers high-value insights without disrupting operations.
Step 2: Reconnaissance
Pentesters gather as much information as possible about your cloud environment — instance types, regions, network segments, access paths, and employed services. This phase helps them map out potential attack surfaces.
Step 3: Vulnerability Scanning
Automated tools are used to scan for common issues: open ports, unpatched services, insecure storage, or IAM misconfigurations. The goal is to build a baseline understanding of typical vulnerabilities.
Step 4: Manual Testing
This is where pentesters play the “attacker” role — trying to exploit weaknesses by chaining together different vulnerabilities. They simulate real attack paths, test privilege escalation, attempt lateral movement, and probe APIs.
Step 5: Exploitation & Privilege Escalation
If a vulnerability is discovered, testers try to exploit it safely — without causing data loss or downtime. They aim to demonstrate the impact of a real breach, including potential data exfiltration or access takeover.
Step 6: Reporting & Recommendations
After testing, the pentest team provides a detailed report containing:
- Found vulnerabilities
- Severity levels
- How each issue can be exploited
- Remediation steps
- Priority ranking for fixing issues
Step 7: Retesting
Once fixes are applied, a retest ensures that vulnerabilities have been properly mitigated. This step validates the improvements and ensures that no new vulnerabilities were introduced.
Key Benefits of Pentest Cloud Services with Opsio Cloud
By partnering with Opsio Cloud, your business gains access to specialized pentest services tailored for cloud environments. Here’s what makes our offering distinct:
- Deep Cloud Expertise: Our team understands the nuances of AWS, Azure, Google Cloud, and hybrid environments.
- Comprehensive Testing: We cover everything from APIs, IAM, VMs, containers, to serverless functions.
- Risk-Based Approach: We focus on real-world risks and business-critical threats, not just technical findings.
- Actionable Remediation: Our reports don’t just identify problems — we suggest practical fixes prioritized by risk.
- Continuous Improvement: With retesting and follow-up assessments, we help you stay secure as your environment evolves.
- Incident Readiness: We help you test your detection and response capabilities so your team is ready if a real attack happens.
Best Practices for Cloud Penetration Testing
Here are some actionable recommendations to get the most out of your pentest:
- Test Regularly: Cloud environments change rapidly. Schedule pentests quarterly or after major changes.
- Integrate with DevOps: Include pentesting in your CI/CD pipeline to catch issues during development.
- Use Least Privilege: Push for strict identity and access controls. Pentesting will help validate policies.
- Enable Logging and Monitoring: Ensure security tools capture all relevant actions — so detection and response are faster.
- Train Your Team: Use pentest findings to improve your incident response procedures and security training.
- Fix and Retest: After addressing issues, always run another test to confirm fixes are effective.
Final Thoughts
Cloud platforms offer enormous advantages, but they also bring new security challenges. Without proactive testing, you’re relying on assumptions — and attackers will happily exploit them. That’s why pentest cloud services are not just a good idea, but a critical part of a modern security posture.
By working with Opsio Cloud, you ensure that your cloud infrastructure is not just protected — it’s resilient. Our expert pentest team will help you uncover vulnerabilities, validate your security controls, and build a safer, stronger cloud foundation.
Read More Gorod